EngramAI: The Trust Layer for
Agentic AI
Enterprise security for AI agents, RAG systems, and MCP servers.
Deploy as multi-tenant SaaS or dedicated single-tenant infrastructure.
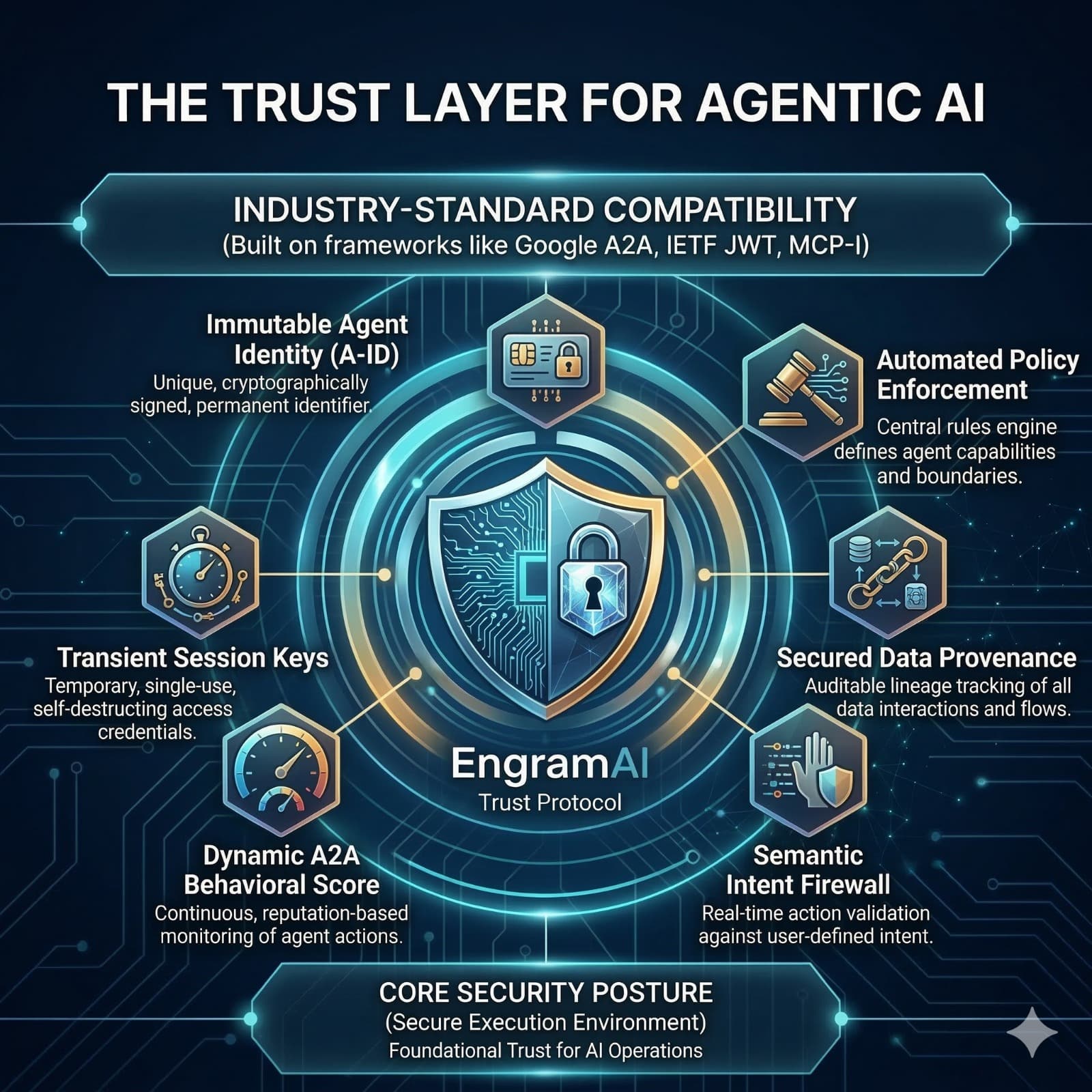
Core Protocol Features
Immutable Agent Identity (A-ID)
Unique, cryptographically signed permanent identifier for every agent
Transient Session Keys
Temporary, single-use, self-destructing access credentials
Dynamic A2A Behavioral Score
Continuous reputation-based monitoring of agent actions
Automated Policy Enforcement
Central rules engine defines agent capabilities and boundaries
Secured Data Provenance
Auditable lineage tracking of all data interactions
Semantic Intent Firewall
Real-time action validation against user-defined intent
Business Value & ROI
AI Agents Are Operating
Without a Trust Framework
Enterprise AI deployments suffer a critical governance gap: agents are granted sweeping, long-lived permissions far exceeding any single task.
The industry average cost of a breach involving AI agents has reached $4.9M per incident.
Broad Permissions
System-wide access regardless of task
Long Lived Credentials
Static keys persist indefinitely
No Verified Identity
No cryptographic attribution
Full System Blast Radius
One compromised agent cascades across infrastructure
Agent Passport
Every AI agent is issued a cryptographic identity credential.
Verifiable, tamper-proof identity bound to:
Three Layers of
Zero Trust Agent Security
Semantic Intent Firewall
Verifies why an agent is acting before execution.
Just-In-Time Credentials
Ephemeral cryptographic keys provisioned per task. Keys self destruct after 60 seconds.
Behavioral Credit Score
Agent reputation system similar to a FICO score. Continuously updated trust score across agent interactions.
Built for Enterprises That
Cannot Afford Failure
Financial Services
SEC, MiFID II, DORA compliant agent attribution
Healthcare
HIPAA safe agent workflows
Public Sector
FedRAMP and CMMC aligned identity verification
SaaS Platforms
Governance layer for AI products
We Don't Build Agents.
We Build The Reason Enterprises Trust Them.
That is the Engram Protocol standard.
See EngramAI in Action
Get a personalized walkthrough of the Defense Layer Platform. See how we protect AI agents, RAG systems, and MCP servers with 100% detection accuracy.
What’s included:
Perfect for:
Enterprise AI Teams
Secure your multi-agent workflows and RAG systems at scale.
Financial Services
Meet compliance requirements with cryptographic audit trails.
AI-Native Companies
Ship faster with confidence. Protect your AI infrastructure from day one.